Intune. Defender. Entra. 💻🛡️👤 Leveraging Microsoft Technology
Aiming to bridge the gap between Microsoft cloud solutions and real-world IT challenges by providing actionable content that helps sys and security admins protect their endpoints and identities with defender and level up their cloud infrastructure with Entra and Intune.
Dynamically Remove Apps from Windows 11 – The New Way
Deploying Windows 11 in an enterprise environment has always come with a small annoyance: You spend time building a clean,...
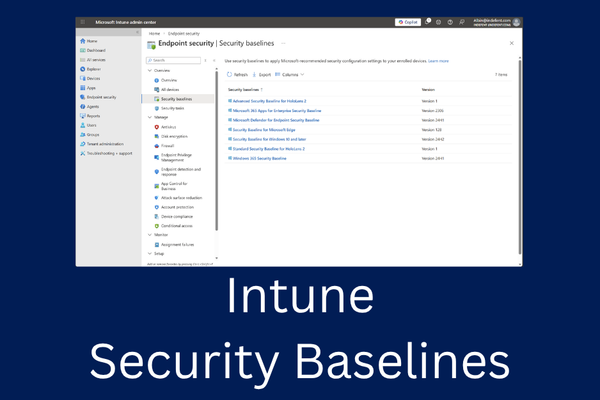
Intune Security Baselines (The 20/80% Rule)
Over the years, I’ve assessed dozens of Intune environments, and one pattern keeps showing up: many IT teams try...
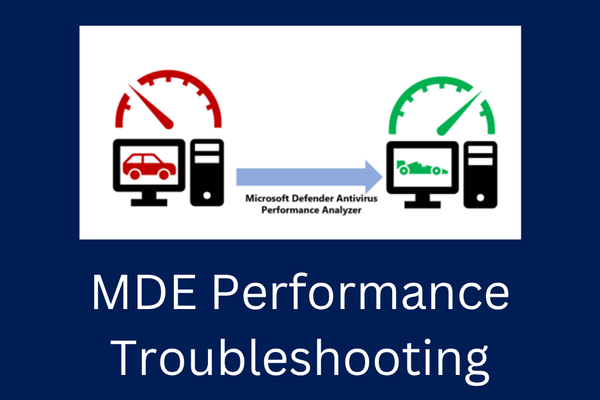
Troubleshooting Performance Bottlenecks in Microsoft Defender for Endpoint
When I implement Microsoft Defender for Endpoint (MDE), I occasionally encounter server teams who report that MDE is slowing down...
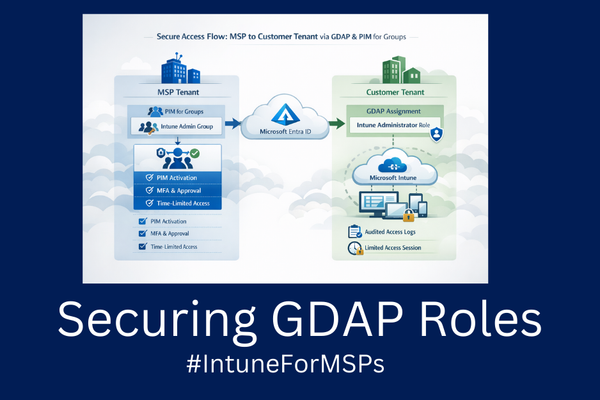
Secure Intune Admin Access with GDAP and PIM for Groups (MSP Edition)
In today’s security landscape, standing administrative privileges are one of the biggest risks especially for MSPs and organizations managing...
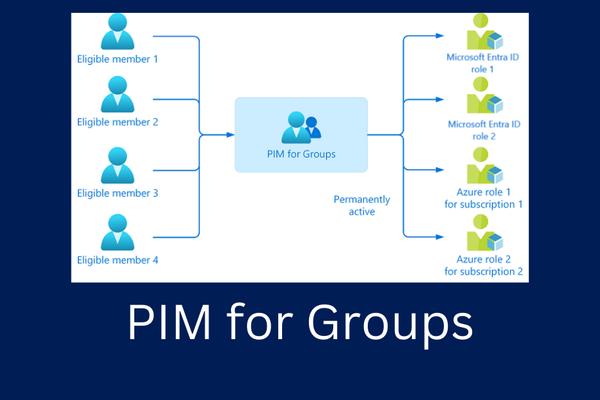
Leveraging PIM for Groups (within Native Cloud & Hybrid Environments)
In Microsoft environments, groups are everywhere. They grant access to SharePoint sites, Azure subscriptions, applications, file shares, and administrative roles...

How to Defender for Office 365 (fast)
Microsoft Defender for Office 365 (MDO) is a cloud-native security solution designed to protect organizations against advanced threats delivered through...

Microsoft Security & Tech Tips in your inbox

- Latest Updates on Intune, Defender, Entra ℹ️
- Insights delivered via email 📥
- Practical Tips for Microsoft security and endpoint management 📢
- Join the awesome Community 🚀